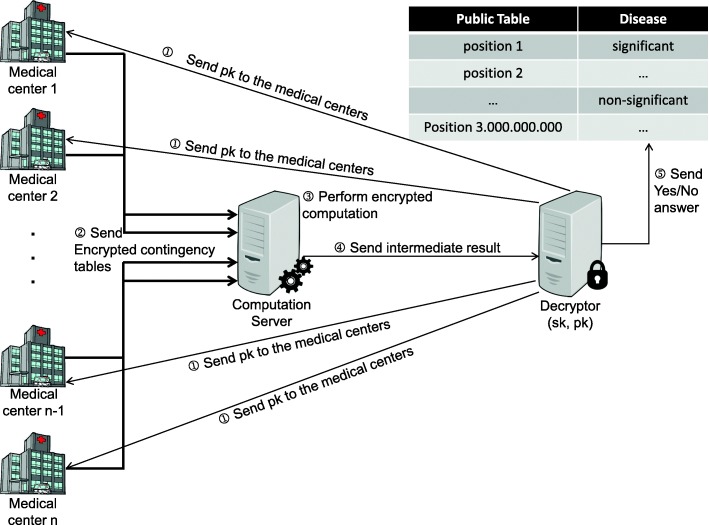
Fig. 1.
A schematic representation of the homomorphic scenario. Before the execution of the protocol, the decryptor generates a valid public and secret key pair for the homomorphic encryption scheme. Step ① of the protocol is to send the generated public key pk to all participating medical centers. Then, the medical centers compute their local contingency tables, encrypt them with the received public key, and send them to computation server in step ②. Step ③ is the actual secure computation of the encrypted, and masked χ2 value, which is then sent to the decryptor in step ④. By decrypting the masked χ2 value (using the secret key sk), the decryptor can only determine whether the result is significant or not, which is published in a public table in step ⑤