. 2018 Sep 9:345–404. doi: 10.1007/978-3-319-95669-5_10
© Springer International Publishing AG, part of Springer Nature 2019
This article is made available via the PMC Open Access Subset for unrestricted research re-use and secondary analysis in any form or by any means with acknowledgement of the original source. These permissions are granted for the duration of the World Health Organization (WHO) declaration of COVID-19 as a global pandemic.
Fig. 10.5.
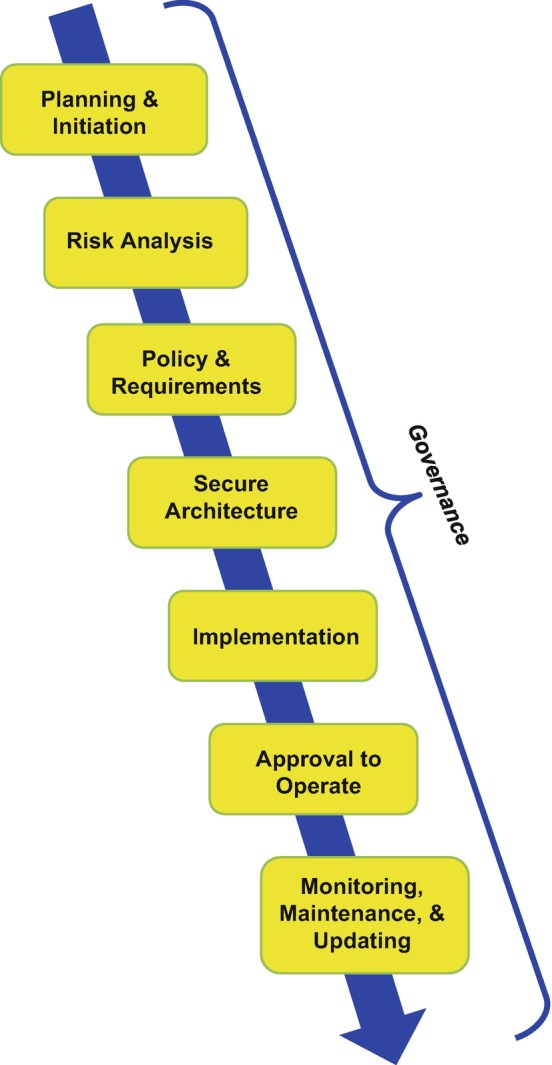
Basic flow of a security architecture process
