Abstract
Designing efficient and secure cryptosystems has been a preoccupation for many scientists and engineers for a long time wherein they use chaotic systems to design new cryptosystems. While one dimensional (1-D) chaotic maps possess powerful properties compared to higher dimension ones, they are vulnerable to various attacks due to their small key space, chaotic discontinuous ranges, and degradation in chaotic dynamical behaviours. Moreover, when simulated on a computer, every such chaotic system produces a periodic cycle. Meanwhile, quantum random walks exhibit the potential for deployment in efficient cryptosystem design, which makes it an excellent solution for this problem. In this context, we present a new method for constructing substitution boxes (S-boxes) based on cascaded quantum-inspired quantum walks and chaos inducement. The performance of the proposed S-box scheme is investigated via established S-box evaluation criterion and outcomes suggest that the constructed S-box has significant qualities for viable applications information security. Further, we present an efficient scheme for pseudo-random numbers generation (PRNG) whose sustainability over long periods remedies the periodicity problem associated with traditional cryptographic applications. Furthermore, by combining the two mechanisms, an atypical image encryption scheme is introduced. Simulation results and analysis validate that the proposed image encryption algorithm will offer gains in many cryptographic applications.
Subject terms: Computer science, Information technology
Introduction
Chaotic systems have attracted a great deal of attention across different scientific and engineering disciplines, especially in designing new cryptosystems and cryptanalysis. A chaotic system is an evolution map of a deterministic dynamical system that reconstructs the state of a system S0 to a new state S1 depending on the initial state of S0, a control parameter C, and time T1. Chaotic maps exhibit the desired properties of ergodicity, unpredictability, and sensitivity to their control parameter(s) and initial value(s) that satisfy the requirements for cryptosystem confusion-diffusion properties2–4. In fact, an inappropriate initial control parameter of a chaotic system can lead to non-chaotic behaviours, which implies the reduction in nonlinearity levels as well as circumvention of insecurity pitfalls5,6.
Currently, chaotic dynamical systems play a vital role in designing modern cryptographic applications, such as constructing S-boxes, generating pseudo-random numbers, designing image encryption algorithms and so on7–16, which are based on the unproven assumptions pertaining to computational complexity and that their constructions are based on mathematical models. However, with the development of quantum technologies, some of these traditional security mechanisms, and cryptographic applications may be effortlessly violated and abused17–19.
Among the computational models developed in quantum computation, quantum walks (QWs), which is a universal model of quantum computation that has been traditionally employed to develop modern quantum algorithms20,21. While physical quantum computing hardware are as yet unavailable, quantum inspired frameworks provide platforms for simulating pseudo-quantum algorithms, which, within the limits of bounds imposed by the capability of digital computers, can to execute some of the quantum mechanical properties ascribed for the potency of quantum computation22–24. Moreover, based on the rationale that computation of the position probability distribution of a quantum walker requires computation of probabilities of frequencies (i.e. the number of detections at a given graph vertex divided by the total number of detections). This requires sufficient number of repetitions of the experiment in order to retrieve the probability distribution. Among others, this has motivated the use of quantum-inspired discrete-time quantum walks have been presented as viable resources useful in designing chaotic system for image encryption algorithms25–29. This procedure allows us to consider a quantum-inspired discrete quantum walk Q as a nonlinear mapping where H is a Hilbert space in which the walker exists and P is a set of probability distributions. At this juncture, we note that our notion of a quantum-inspired approach implies use of probability distribution of a quantum walk obtained from numerical simulations using digital resources.
The nonlinear behaviour of quantum-inspired walks described above together with the deterministic nature of state growth via unitary operators as well as the high sensitivity of quantum walks to initial conditions support the treatment of quantum-inspired discrete quantum walks as discrete-time and discrete-value chaotic systems25,26,30.
Inspired by the excellent dynamical properties of quantum walks, the limitations of traditional cryptosystems can be ameliorated via design and construction state-of-the-art techniques for effective information security applications. In addition to other benefits, a main contribution of this study is to explore the integration of quantum-inspired of quantum walks into traditional cryptographic applications. Hence, we present a bi-level cascaded quantum walks protocol as a quantum-inspired random number generator with chaos inducement. The performance of the proposed S-box scheme is investigated using established criterions, results of which suggest that the constructed S-box is viable for multifaceted applications in information security. Similarly, the analyses of the proposed PRNG suggest its efficiency in generating sequences that remedy the periodicity problem associated with traditional cryptographic applications. Finally, we deploy the dual cascade quantum walks and chaos systems for applications in image encryption. Throughout, simulation-based validation is used to assess the performance of the proposed scheme. Outcomes from our applications for S-boxes construction, pseudo-random number generation, and image encryption validate the choice of cascaded quantum walks and chaos inducement for various cryptographic applications. At this point we clarify that this study is focused on exploiting properties of quantum walks for use in a quantum-inspired setting for potential applications in traditional cryptography. Hence, the quantum mechanical implementation of quantum walks is deemed outside the purview of this present work. Nevertheless, we enrich our bibliography by including interesting studies on such implementation19,20,31–40 from where interested readers can obtain further details.
Results
S-box construction
Designing powerful S-boxes is an important critereon for realisation of secure cryptosystems and it is a major component of nonlinear transformations, which are the fulcrum of confusion and diffusion analysis for assessing well-designed ciphers41. Therefore, designing S-boxes based on secure mechanisms plays an important part in modern cryptographic tasks42,43. Consequently, it is widely investigated. For example, in a recent effort EL-Latif el al.30 explored construction of secure S-boxes based on one-dimensional two-walker QWs on a circle. Inspired by the potency of quantum technologies, in this section, we propose a mechanism to augment some shortcomings of standard S-box construction and integrate our upgraded design into a cascaded QW and chaos inducement system for designing efficient cryptographs.
The following steps outline the construction of an M-length S-box.
Step 1: Choose initial seed for x0 and a value for the control parameter λ, to iterate the logistic-sine map over N times needed to generate sequence .
Step 2: Choose initial conditions and key parameters () for running QWs on a circle with v vertices to produce a probability matrix , where v is odd number, and t is the number of steps for running QWs. Hence, the coin operator constructed by the key parameters and , while the initial states of the two walkers are and , respectively.
Step 3: Resize P to QWN, where N is the number of iterated chaos map. Here, we recall that mathematically no error arises from scaling a matirix with fixed dimentions several times. Targeting such a property, in this step, we make use of the bicubic interpolation resizing44, which has zero error during the scalling process etc. This attribute allows it to accommodate prolonged iterations in the chaos map generation.
Step 4: Convert the sequences , and into integer values via Eqs. (1) and (2).
| 1 |
| 2 |
Step 5: Perform the bitwise XOR operation on the sequences , and to produce the sequence with range from 0 to M-1.
Step 6: Collate the first M dissimilar elements from the sequence to construct the desired S-box.
The performance of the S-box construction technique is investigated using a workstation equipped with Intel® core™ i5-2450M CPU 2.5 GHz and 6 GB RAM with a preinstalled MATLAB software. The initial values for running QWs are set as , , , , , , while initial values used to iterate the logistic-sine map are set as , .
The constructed 16 × 16 S-box costructed based on the aforesaid initial conditions and control parameters is presented in Table 1, while Table 2 provides comparison of the performance of the constructed S-box alongside those some published schemes alongside the proposed one in terms of standard parameters of strict avalanche (SAC), nonlinearity, bit independence (BIC), as well as differential (DP) and linear (LP) approximation probabilities.
Table 1.
16 × 16 S-box constructed via proposed scheme.
| 205 | 51 | 93 | 103 | 62 | 198 | 199 | 224 | 149 | 114 | 75 | 48 | 132 | 102 | 142 | 125 |
| 204 | 173 | 253 | 23 | 180 | 65 | 245 | 50 | 208 | 118 | 117 | 121 | 156 | 38 | 152 | 138 |
| 193 | 128 | 243 | 127 | 105 | 96 | 4 | 154 | 76 | 251 | 196 | 169 | 95 | 120 | 190 | 98 |
| 211 | 179 | 175 | 188 | 81 | 219 | 41 | 84 | 218 | 195 | 200 | 153 | 248 | 209 | 36 | 207 |
| 30 | 157 | 183 | 67 | 143 | 194 | 135 | 133 | 64 | 236 | 3 | 33 | 254 | 86 | 49 | 79 |
| 227 | 240 | 249 | 104 | 163 | 250 | 115 | 78 | 74 | 68 | 178 | 17 | 162 | 159 | 12 | 139 |
| 18 | 11 | 164 | 191 | 61 | 235 | 87 | 181 | 222 | 113 | 108 | 226 | 106 | 221 | 37 | 241 |
| 29 | 177 | 174 | 2 | 6 | 202 | 99 | 92 | 184 | 158 | 172 | 171 | 0 | 242 | 215 | 28 |
| 40 | 5 | 189 | 214 | 206 | 24 | 165 | 110 | 26 | 155 | 246 | 14 | 111 | 230 | 237 | 52 |
| 69 | 182 | 59 | 122 | 197 | 231 | 116 | 234 | 56 | 35 | 167 | 13 | 101 | 126 | 27 | 210 |
| 42 | 119 | 91 | 60 | 147 | 216 | 166 | 89 | 203 | 112 | 53 | 55 | 71 | 124 | 39 | 130 |
| 85 | 31 | 72 | 19 | 45 | 185 | 168 | 150 | 186 | 90 | 22 | 212 | 1 | 15 | 107 | 141 |
| 140 | 144 | 77 | 151 | 131 | 232 | 238 | 247 | 136 | 217 | 233 | 58 | 21 | 145 | 88 | 225 |
| 129 | 228 | 201 | 146 | 255 | 46 | 32 | 7 | 44 | 82 | 70 | 20 | 97 | 43 | 83 | 134 |
| 187 | 10 | 239 | 34 | 47 | 137 | 109 | 229 | 252 | 213 | 161 | 94 | 123 | 170 | 160 | 63 |
| 80 | 220 | 57 | 148 | 9 | 16 | 54 | 25 | 100 | 244 | 73 | 66 | 8 | 176 | 192 | 223 |
Table 2.
Evaluation of the performance of proposed S-box construction alongside other methods.
| S-box scheme | BIC-NL | Nonlinearity | BIC-SAC | SAC | LP | DP |
|---|---|---|---|---|---|---|
| Proposed | 103.93 | 106 | 0.5023 | 0.4958 | 0.1250 | 0.0313 |
| EL-Latif et al.30 | 103.70 | 106.25 | 0.5065 | 0.5037 | 0.1016 | 0.0391 |
| Belazi et al. S-box61 | 103.78 | 105.50 | 0.4970 | 0.5000 | 0.1250 | 0.0468 |
| Khan et al.62 | 103.07 | 103.25 | 0.4864 | 0.5151 | 0.1563 | 0.17187 |
| Wang et al. S-box63 | 103.36 | 104.87 | 0.5017 | 0.4918 | 0.1328 | 0.0391 |
| Tang et al. et al.64 | 103.00 | 105.00 | 0.5044 | 0.4971 | 0.1328 | 0.0391 |
| Özkaynak et al.65 | 103.14 | 104.62 | 0.4942 | 0.4982 | 0.1406 | 0.0391 |
| Belazi et al.66 | 103.80 | 105.25 | 0.4996 | 0.4956 | 0.1562 | 0.0391 |
| Hussain et al.67 | 104.29 | 103.25 | 0.5021 | 0.5056 | 0.1289 | 0.04609 |
PRNG generator
Pseudo-random number generation (PRNG) plays a fundamental role in creating powerful cryptographic schemes and, as such, they attract a great deal of attention from many cryptographers and engineers. The key feature of PRNG is to provide long streams of numbers embedded with randomness features. PRNG has a vital impact on the robustness of cryptographic tasks and in mitigating attempts to violate, tamper with, or regenerate the secret information being protected. The common approach employed in designing PRNG generators is based on using chaos maps, which is a simple (in terms of definition), yet disorienting approach intended to circumvent infractions to sensitive information9,11. Previous efforts, such as45, profit from the utility of quantum walks to overcome established limitations of traditional chaos maps. Furthermore, Yang et al.45 proposed a novel PRNG mechanism based on quantum walks.
Motivated by the effort in45, in this section, we discuss our proposed mechanism for PRNG sequence generation whose outline is presented in Fig. 1 and execution is accomplished via the five steps enumerated in the sequel.
Figure 1.

Outline of the proposed PRNG sequence generation mechanism.
Step 1: Select initial seed for and a value for the control parameter , to iterate the logistic-sine map over N times needed to generate sequence .
Step 2: Select initial conditions and key parameters () for running QWs on a circle with v vertices to produce a probability matrix , where v is odd number, and t is the number of steps for running QWs. Hence, the coin operator constructed by the key parameters and , while the initial states of the two walkers are and , respectively.
Step 3: Resize to , where N is the number of iterations for the chaos map as well as the length of desired PRNG sequence.
Step 4: Convert the sequences , and into integer values as follows:
Step 5: Perform bitwise XOR operation on the sequences , and to generate a PRNG sequence, S of length N.
To investigate the randomness property of the generated PRNG sequence S, we applied NIST SP 800-22 specified tests. These tests comprise of fifteen (15) assessments that are performed on a generated sequence of 106 bits length. We used the same initial values and control parameters for constructing S-box to generate the PRNG sequence whose results are presented in Table 3. As seen therefrom, the sequence generated via the proposed mechanism excelled in all tests carried out; thus, confirming its utility across various cryptographic applications.
Table 3.
Results for NIST SP 800-22 tests.
| Test-Name | P-Value | Result |
|---|---|---|
| Overlapping templates | 0.215108 | Passed |
| No overlapping templates | 0.079004 | Passed |
| DFT | 0.304052 | Passed |
| Frequency | 0.291883 | Passed |
| Block-frequency | 0.693686 | Passed |
| Universal | 0.612656 | Passed |
| Rank | 0.058737 | Passed |
| Long runs of ones | 0.137157 | Passed |
| Runs | 0.384907 | Passed |
| Serial 1 | 0.914512 | Passed |
| Serial 2 | 0.971079 | Passed |
| Random excursions variant x = 1 | 0.506620 | Passed |
| Random excursions x = 1 | 0.125622 | Passed |
| Linear complexity | 0.107102 | Passed |
| Cumulative sums (reverse) | 0.065686 | Passed |
| Cumulative sums (forward) | 0.520534 | Passed |
| Approximate entropy | 0.012095 | Passed |
Application of proposed cascade protocol in image encryption
The intuition to utilise chaos systems in image encryption is not new, including many employing one-dimensional or higher dimension chaotic systems to generate a sequence of random numbers for construction of a cipher image that have been broached in12–16. However, most of these approaches produce images that are vulnerable to various attacks due to their narrow key-space allowance and imprecise mathematical construction. Consequently, to ameliorate this, some interesting image encryption algorithms based on the dynamical properties of QWs were proposed in25,26 and27.
In this section, we exploit the potency of quantum computing technologies to ameliorate some established shortcomings inherent to existing chaos systems. Our proposed image encryption technique utilises the S-box construction and PRNG sequence generation methods presented in earlier sections of this study to substitute and permutate each pixel of a plain image and construct its encrypted version. These procedures and their perfomance analysis are further elucidated in the remainder of this section.
The general framework for the proposed image encryption technique is illustrated in Fig. 2, while the encryption procedures are outlined in the following steps.
Select initial values for generating two S-boxes SH and SW of lengths h and w respectively, where the size of the original image is h × w.
Select initial values for generating one PRNG sequence K of length h × w (or h × w × 3 for colour images) where the size of the original image is h × w.
Perform bitwise XOR operation on original image and matrix K to obtain an Xored image.
Permutate the Xored image using the constructed S-boxes as outlined in Algorithm 1.
Algorithm 1.
Image encryption algorithm.
Figure 2.

General framework for the proposed image encryption technique.
Performance analysis
To validate the proposed strategy, we simulated implementation of the image encryption algorithm using a dataset comprising of three greyscale (Bridge, Boat and Baboon) and three colour images (Sailboat, Tree and House) sourced from the Signal and Image Processing Institute dataset46 and each of 256 × 256 dimensions. These test images are presented in Fig. 3(a–f). Initial values for running the QWs to construct S-boxes and generate PRNG sequences were set at , , , , , , while initial values used to iterate the logistic-sine map are set as , .
Figure 3.

Test images (a–f), their encrypted (in (g–l)), and decrypted (in (m–r)) versions.
The resulting encrypted versions of the test images are presented in Fig. 3(g–m) and based on the pairing of each original and encrypted image pair we undertook a retinue of statistical analysis whose results are presented and discussed in subsequent subsections.
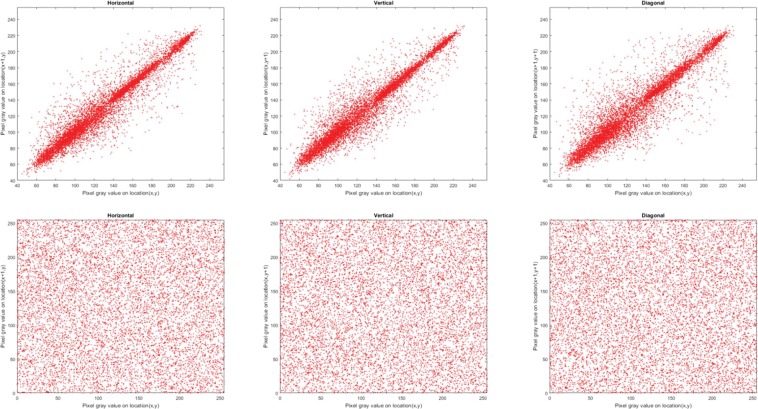
Correlation of adjacent pixels
Correlation coefficient, Cxy, is used to measure concordance between two adjacent pixels X and Y in an image. Theoretically, a pristine, i.e. unencrypted, image should have Cxy values close to 1 in each direction (horizontal, vertical and diagonal) whereas a well encrypted image should have values close to 047–49. To compute Cxy for the encrypted and original images in each direction, we randomly selected 10,000 pairs of neighbouring pixels and used (3) to quantify their correlation.
| 3 |
where and are values of adjacent pixels and M is the total number of adjacent pixel pairs in each direction. Tables 4 and 5 present the values of Cxy for the encrypted and corresponding original images, where the encrypted images have Cxy values close to 0. The distribution of neighbouring pixel pairs in each direction of Bridge image are graphed in Fig. 4, while those for the R, G, and B channels of the Sailboat colour image are presented in Figs. 5, 6 and 7, respectively. The results in Tables 4 and 5 as well as those in Figs. 4, 5, 6 and 7 suggest that for the three pairs reported there is no relation between the encrypted images and their original versions.
Table 4.
Correlation coefficients for adjacent pixel pairing for greyscale images (in Fig. 3(a–c)).
| Image | Direction | ||
|---|---|---|---|
| Horizontal | Vertical | Diagonal | |
| Original (Bridge) | 0.9160 | 0.9416 | 0.8845 |
| Encrypted (Bridge) | 0.0002 | 0.0026 | −0.0003 |
| Original (Boat) | 0.9436 | 0.9246 | 0.8811 |
| Encrypted (Boat) | −0.0034 | −0.0043 | −0.0012 |
| Original (Baboon) | 0.8304 | 0.8776 | 0.7963 |
| Encrypted (Baboon) | −0.0050 | 0.0001 | 0.0006 |
Table 5.
Correlation coefficients for adjacent pixel pairing for colour images (in Fig. 3(d–f)).
| Image | Direction | ||||||||
|---|---|---|---|---|---|---|---|---|---|
| Horizontal | Vertical | Diagonal | |||||||
| R | G | B | R | G | B | R | G | B | |
| Original (Sailboat) | 0.9552 | 0.9555 | 0.9644 | 0.9582 | 0.9567 | 0.9606 | 0.9311 | 0.9249 | 0.9373 |
| Encrypted (Sailboat) | −0.0003 | −0.0082 | −0.0003 | −0.0022 | −0.0020 | 0.0047 | 0.0013 | 0.0004 | 0.0010 |
| Original (Tree) | 0.9392 | 0.9485 | 0.9438 | 0.9584 | 0.9696 | 0.9615 | 0.9221 | 0.9339 | 0.9308 |
| Encrypted (Tree) | −0.0029 | −0.0048 | −0.0023 | −0.0013 | −0.0012 | −0.0050 | −0.0007 | 0.0012 | −0.0061 |
| Original (House) | 0.9357 | 0.9636 | 0.9764 | 0.9678 | 0.9812 | 0.9824 | 0.9107 | 0.9490 | 0.9641 |
| Encrypted (House) | 0.0027 | −0.0081 | −0.0009 | −0.0023 | 0.0005 | 0.0030 | −0.0040 | 0.0007 | −0.0029 |
Figure 4.
Correlation distribution for neighbouring pixel pairs along horizontal, vertical and diagonal directions for Bridge image in Fig. 3(a).
Figure 5.
Correlation distribution for neighbouring pixel pairs along horizontal, vertical and diagonal directions for red channel of Sailboat image in Fig. 3(d).
Figure 6.
Correlation distribution for neighbouring pixel pairs along horizontal, vertical and diagonal directions for green channel of Sailboat image in Fig. 3(d).
Figure 7.
Correlation distribution for neighbouring pixel pairs along horizontal, vertical and diagonal directions for blue channel of Sailboat image in Fig. 3(d).
Pixel change rate
Another tool used to evaluate the effect of changing pixel values in an original image on its corresponding encrypted one is number of pixel change rate (NPCR), which is computed using (4).
| 4 |
where M denotes total number of pixels in the image. The fact that, as reported in Table 6, all the test images (in Fig. 3(a–f)) produced NPCR values of approximately 99.60% shows that the proposed encryption strategy is very sensitive to small changes in pixel values in the original image.
Table 6.
NPCR test results.
| Image | NPCR (%) |
|---|---|
| Bridge | 99.63837 |
| Boat | 99.59717 |
| Baboon | 99.61395 |
| Sailboat | 99.61853 |
| Tree | 99.61294 |
| House | 99.60124 |
Histogram analysis
Histogram analysis is another widely used measure in image analysis that reflects the frequency distribution of pixel values in an image. A well-designed image encryption algorithm should have uniform histograms for different encrypted images, which is an indication of resistance against statistical attacks. Figures 8 and 9 present histograms for the original and encrypted versions of the greyscale images (in Fig. 3(a–c)) as well as the coloured colour Sailboat image in Fig. 3(d). Interpreting these plots, we deduce similarity in the distribution for the encrypted images. This is an affirmation that the encrypted images consist of flat-out noise. Meanwhile, the variability in the histograms of the original images indicate the presence of different levels of detail in those images. From the histogram analysis there is no relation between the encrypted image and its original one. Therefore, the proposed image encryption mechanism could resist histogram analysis attacks.
Figure 8.
Histograms of original and encrypted greyscale images (in Fig. 3(a–c)).
Figure 9.
Histograms of original and encrypted R, G, and B channels of the Sailboat image (in Fig. 3(d)).
Information entropy
Information entropy, E(X), is an important tool to evaluate the efficiency of an image encryption algorithm. As expressed in (5), E(X) is a statistical measure of the distribution of pixel values for each level in an image.
| 5 |
where is the probability of obtaining . Greyscale images have 28 possible values based on which the ideal theoretical entropy value should be 8 bits27. Consequently, for an efficient encryption mechanism, the entropy value for the encrypted images should be close to 8. Table 7 presents the entropy values for the pristine and corresponding encrypted images used in our experiments (i.e. Fig. 3). As targeted, the information entropies for almost all the pairings is expected to be 8 bits (Table 7). This certifies the viability of the proposed algorithm to withstand entropy-based attacks.
Table 7.
Information entropy of original and encrypted images.
| Image | Original | Encrypted |
|---|---|---|
| Bridge | 7.66847 | 7.99710 |
| Boat | 7.15866 | 7.99734 |
| Baboon | 7.22794 | 7.99729 |
| Sailboat | 7.35408 | 7.99727 |
| Tree | 7.18159 | 7.99700 |
| House | 6.40067 | 7.99704 |
Key space analysis
Theoretically, quantum-inspired quantum walks have an infinite key space25,26,45, but due to the finite precision of digital computers, the key space is limited. Therefore, the key space size is evaluated relative to the 10−16 precision of digital computers, which is acceptable for quantum insipired numerical simulation of quantum walks on digital computers50,51. However, it is highly unrealistic for actual physical implementation of a quantum walk, which would be the goal of future quantum technologies. Nevertheless, such simulation would suffice for classical-based quantum inspired simulation of our proposed random number generator.
A well-designed encryption algorithm should have adequate key space allowance to withstand brute-force and other attacks intended to violate its integrity. In our algorithm, a plain-image is substituted with a PRNG sequence (from the presented PRNG mechanism), while the proposed S-box mechanism is used to permutate each pixel of the substituted image, which combined coalesces as the encrypted image. Therefore, in addition to possessing key parameters for generating PRNG, the proposed algorithm is ingrained with key space needed for constructing the S-boxes (key parameters are used both for generating PRNG sequence and constructing S-box). Since both the PRNG sequence generation and S-box construction schemes are components of the proposed cascade quantum-inspired quantum walks on a circle and logistic-sine map technique, which both possess key parameters (), then the key space for generating PRNG or constructing S-boxes is 10128 and, therefore, the key space allowance for the image encryption algorithm presented earlier is 10256, which is adequate for any encryption algorithm. Table 8 provides a comparison of key spaces for the proposed mechanism in comparison with similar approaches. Outcomes therefrom demonstrate our proposed mechanism has a superior key space allowance.
Table 8.
Description of key space of our presented mechanism alongside those from similar methods.
| Algorithm | Description | Key space |
|---|---|---|
| Proposed | Cascaded quantum walks as a quantum-inspired random generator and chaotic dynamics induction with its cryptographic applications | Key parameters (v, t, α1, α2, β1, β2, x0, λ) are utilised to run QWs and iterate logistic-sine map. The encryption algorithm is based on the presented PRNG mechanism and S-box mechanism. Therefore, the key space of whole system is 10256. |
| Yang et al.45 | PRNG mechanism based on running 1-Dimensional 1-Particle quantum walks on a circle | Key parameters (v, t, α, β, θ) are utilized for running QWs. The key space for key parameters and initial states is 1098. |
| Yang et al.25 | Image encryption algorithm based on running 1-Dimensional 2-Particle quantum walks on a circle | The key parameters (v, t, α1, β1, α2, β1, θ) are utilized for running QWs. The key space for key parameters is 1098. |
| Yang et al.26 | Quantum hash function based on controlled 1-Dimensional 2-Particle quantum walks on a circle with its application to image encryption | Key parameters (m, v, α1, β1, α2, β1) are utilized for running QWs. The key space for key parameters and initial states is 1098. |
| Abd-El-Atty et al.27 | Quantum greyscale image encryption algorithm based on controlled 1-Dimensional 1-Particle quantum walks on a circle | Key parameters (m, v, t, α, β, θ1, θ2, θ3) are used for running QWs. The key space of whole system is roundly 10211. |
As suggested by the guideline in52 key space must be greater than for it to exhibit sufficient security against brute-force attacks. In our case, the proposed approach has a key space of 10256 which consists of all possible keys. Consequently, to mitigate against the exhaustive search-attacks, a good cipher should have a key space size of . This conforms with earlier guidelines in25,26,45. Based on the proposed approach, we can conclude that key size 10256 is adequate to forestall brute-force attacks in today’s and near future’s computers.
Key sensitivity analysis
To test the key sensitivity of the proposed image encryption algorithm, we demonstrate the decryption process for the encrypted Bridge and Sailboat images using several keys for constructing S-boxes and generating PRNG sequences. The results obtained therefrom are presented in Figs. 10 and 11, where Figs. 10(a) and 11(a) demonstrate near zero error during the scaling process for the probability matrix P.
Figure 10.
Decrypted Bridge image (in Fig. 3(g)) for several S-box keys.
Figure 11.
Decrypted Sailboat image for several PRNG keys.
Discussion
Discrete-time quantum random walks are regarded as nonlinear mappings between quantum states and position probability distributions. They provide an imprint of chaotic behaviour, which are mathematical properties that can be exploited in constructing robust cryptographic applications. The study presented explores the potential for deploying quantum-inspired quantum random walks (QiQw) in the design of efficient cryptosystems. We have presented three quantum-inspired mechanisms that cascade quantum walks as a random number generators with logistic-sine map to ameliorate problems of periodicity in chaotic ranges, narrow key space and chaotic discontinuous ranges that are associated with traditional cryptosystems. First, we presented a mechanism for constructions of S-boxes with prospects for wide-ranging applications in security technologies. Second, we proposed a scheme to generate PRNG sequences that remedy the periodicity problem encountered in cryptographic applications. Third, we coalesced the two strategies into a cascaded quantum walks on a circle with logistic-sine map and implemented it as an image encryption algorithm. Based on simulations of our proposed schemes, we undertook extensive statistical analysis to validate the efficiency, reliability and utility of our proposed techniques alongside established methods employed in different cryptographic applications. With further improvements, the study presented provides useful insights to integrate state-of-the-art quantum-inspired quantum resources into building efficient, secure, and robust future cryptography technologies.
Methods
Rudimentary background required for basic understanding of the proposed cascade quantum-inspired quantum walks and chaos system are highlighted in this section. Furthermore, a succinct overview on the execution of discrete-time quantum walks on a circle as well as the utility of logistic-sine map as a chaos system are expounded.
Discrete-time quantum walks on a circle
Unlike in classical (i.e. digital or non-quantum) walks, the state of a quantum walk is a coherent superposition of several positions (quantum superposition of quantum walks)53, but much like their classical (i.e. digital) equivalents, there are two categories of quantum walks: discrete-time quantum walks and continuous-time quantum walks20. In this study, we focus on discrete-time quantum walks (or simply QWs), which have shown viability in wide-ranging cryptographic applications18,19,25,26,28,30,45,54–58. QWs have two basic parts: the walker space Hp and the coin particle , which permeates a Hilbert space . The initial state of the system can be transformed into another state via application of the evolution operator for the whole quantum system
| 6 |
where refers to the shift operator that depends on the coin state of the particle, which can be defined on a circle with v vertices as presented in Eq. (7).
| 7 |
The operator refers to a 2 × 2 coin operator, whose general case can be defined in (8).
| 8 |
Hence, the final state after t steps can be expressed as
| 9 |
The probability of finding the walker at position x after t steps can be stated as
| 10 |
where is the initial state of the quantum system, and .
Another attractive characteristic of multi-walker quantum random walks is that, in the case of interacting walkers, the dimension of the Hilbert space of an n-particle quantum walk (composed of distinguishable walkers) increases exponentially with the number of walkers, a property that supports increased entanglement. These properties are unattainable in classical random walks. Consequently, in our proposed model, the impetus for use of two instead of one quantum walker is its offer of increased keyspace allowance, which is crucial for designing efficient cryptosystems. Further details on interacting two quantum walks on a circle can be obtained from19,59.
In our proposed model of quantum walks, two coins , and two walkers , will be used. The combined shift operator for the system is 19,25,26, where and are shift operators for and , respectively. Following the same rationale, we shall use two coin operators, one for each coin , . Therefore, the combined coin operator is a Unitary operator that can be written as an order 4 matrix19,25,26. In this study, we have chosen the coin matrices presented in Eq. 11.
| 11 |
An example illustrating the probability distributions of running one-dimensional two-particle quantum walks on a circle with 11 vertices is presented in Fig. 12, where the initial position is and the initial coin operator constructed by and in formats stated in Eq. 11. It is obvious that, for a circle with only odd v nodes, the probability is nonzero in any position if the number of steps t is greater than or equal to the number of nodes v. In this study, we utilised the probability distribution generated from using quantum-inspired two-walker quantum walks in the cascading system whose construction is based on the coherent superposition of several positions of quantum walks rather than constructions from a mathematical model as obtains in chaotic maps. Like other quantum measurement operations, measurements to recover states of quantum walks, involve retrieval of probability distributions by repeating the measurement process many times, which is not completely accurate. Meanwhile, as clarified in our introductory commentary, our notion of quantum-inspired quantum walks entails the use of probability distributions that are obtained via numerical simulations using digital resources. Nevertheless, like any cryptographic mechanism, if the key parameters of the quantum-inspired quantum walk are disclosed, then anyone can access the probability distribution with appreciable precision. On the other hand, if the parameters are unknown, but a part of the probability distribution is disclosed, then it is very difficult to estimate the key parameters or the recover the probability distribution because our quantum-inspired quantum walk is a one-way mechanism18,19,26. Consequently, it is envisioned that the suggested cryptographic applications would offer additional layers of tamper-proof security within the precepts of quantum-inspired quantum walks.
Figure 12.

Probability distribution for running two-walker quantum walks on a circle with 11 vertices for 51 steps, where the initial coin particles are and . Here, it is deducible that for a circle with only odd v nodes, the probability has nonzero in any position if the number of steps t is greater than the number of nodes v.
Discrete-time chaotic systems
As argued in earlier sections of this study, one-dimensional chaotic maps are considered in this study because they offer enhanced periodicity in chaotic ranges, narrow key space and chaotic discontinuous ranges when it is used in cryptographic systems60. However, the same one-dimensional chaotic maps exhibit powerful benefits in terms of high-speed processing, easy design and simple structure.
A widely used one-dimensional chaotic map is logistic-sine map16, which is expressed mathematically as
| 12 |
where is the control parameter, and x0 is the initial condition.
Depending on the set of times T, chaotic dynamical systems can be divided into two classes, i.e. either continuous-time dynamical system (i.e. when T = R) or discrete-time dynamical system (if T = Z). Our study focuses on applying chaotic dynamical systems defined in discrete time, since they possess low computational complexity and do not need synchronization as in continuous-time dynamical system1–3.
Acknowledgements
This study is sponsored by the Prince Sattam Bin Abdulaziz University, Saudi Arabia via the Deanship for Scientific Research funding for the Advanced Computational Intelligence & Intelligent Systems Engineering (ACIISE) Research Group Project Number 2019/01/9862. Also, A.A. Abd El-Latif acknowledges the support of TYSP-Talented Young Scientist Program (China) and Menoufia University (Egypt).
Author contributions
A.A. Abd El-Latif and B. Abd-El-Atty conceived and conducted the experiments, A.A. Abd El-Latif, M. Amin and A.M. Iliyasu analysed the results and wrote the manuscript. All authors reviewed and approved the manuscript.
Competing interests
The authors declare no competing interests.
Footnotes
Publisher’s note Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Contributor Information
Ahmed A. Abd El-Latif, Email: a.rahiem@gmail.com
Abdullah M. Iliyasu, Email: a.iliyasu@psau.edu.sa
References
- 1.Li C, Feng B, Li S, Kurths J, Chen G. Dynamic analysis of digital chaotic maps via state-mapping networks. IEEE Trans. Circuits Syst. I: Regul. Pap. 2019;66:2322–2335. doi: 10.1109/TCSI.2018.2888688. [DOI] [Google Scholar]
- 2.Matthews R. On the derivation of a âchaoticâ encryption algorithm. Cryptologia. 1989;13:29–42. doi: 10.1080/0161-118991863745. [DOI] [Google Scholar]
- 3.Kocarev, L. & Lian, S. Chaos-based cryptography: Theory, algorithms and applications, vol. 354 (Springer Science & Business Media, 2011).
- 4.Jallouli O, El Assad S, Chetto M, Lozi R. Design and analysis of two stream ciphers based on chaotic coupling and multiplexing techniques. Multimed. tools Appl. 2018;77:13391–13417. doi: 10.1007/s11042-017-4953-x. [DOI] [Google Scholar]
- 5.Li C, Lin D, Lü J, Hao F. Cryptanalyzing an image encryption algorithm based on autoblocking and electrocardiography. IEEE Multimed. 2018;25:46–56. doi: 10.1109/MMUL.2018.2873472. [DOI] [Google Scholar]
- 6.Li C, Lin D, Feng B, Lü J, Hao F. Cryptanalysis of a chaotic image encryption algorithm based on information entropy. IEEE Access. 2018;6:75834–75842. doi: 10.1109/ACCESS.2018.2883690. [DOI] [Google Scholar]
- 7.Zhou Y, Hua Z, Pun C-M, Chen CP. Cascade chaotic system with applications. IEEE Trans. Cybern. 2014;45:2001–2012. doi: 10.1109/TCYB.2014.2363168. [DOI] [PubMed] [Google Scholar]
- 8.Lv X, Liao X, Yang B. A novel pseudo-random number generator from coupled map lattice with time-varying delay. Nonlinear Dyn. 2018;94:325–341. doi: 10.1007/s11071-018-4361-4. [DOI] [Google Scholar]
- 9.Murillo-Escobar M, Cruz-Hernández C, Cardoza-Avendaño L, Méndez-Ramrez R. A novel pseudorandom number generator based on pseudorandomly enhanced logistic map. Nonlinear Dyn. 2017;87:407–425. doi: 10.1007/s11071-016-3051-3. [DOI] [Google Scholar]
- 10.Sahari ML, Boukemara I. A pseudo-random numbers generator based on a novel 3d chaotic map with an application to color image encryption. Nonlinear Dyn. 2018;94:723–744. doi: 10.1007/s11071-018-4390-z. [DOI] [Google Scholar]
- 11.Lambić D. Security analysis and improvement of the pseudo-random number generator based on quantum chaotic map. Nonlinear Dyn. 2018;94:1117–1126. doi: 10.1007/s11071-018-4412-x. [DOI] [Google Scholar]
- 12.El-Latif AAA, Li L, Wang N, Han Q, Niu X. A new approach to chaotic image encryption based on quantum chaotic system, exploiting color spaces. Signal. Process. 2013;93:2986–3000. doi: 10.1016/j.sigpro.2013.03.031. [DOI] [Google Scholar]
- 13.Belazi A, El-Latif AAA, Belghith S. A novel image encryption scheme based on substitution-permutation network and chaos. Signal. Process. 2016;128:155–170. doi: 10.1016/j.sigpro.2016.03.021. [DOI] [Google Scholar]
- 14.Li, L., Abd-El-Atty, B., El-Latif, A. A. A. & Ghoneim, A. Quantum color image encryption based on multiple discrete chaotic systems. In 2017 Federated Conference on Computer Science and Information Systems (FedCSIS), 555–559 (IEEE, 2017).
- 15.Luo Y, Zhou R, Liu J, Cao Y, Ding X. A parallel image encryption algorithm based on the piecewise linear chaotic map and hyper-chaotic map. Nonlinear Dyn. 2018;93:1165–1181. doi: 10.1007/s11071-018-4251-9. [DOI] [Google Scholar]
- 16.El-Latif AAA, Abd-El-Atty B, Talha M. Robust encryption of quantum medical images. IEEE Access. 2017;6:1073–1081. doi: 10.1109/ACCESS.2017.2777869. [DOI] [Google Scholar]
- 17.Kiktenko EO, et al. Quantum-secured blockchain. Quantum Sci. Technol. 2018;3:035004. doi: 10.1088/2058-9565/aabc6b. [DOI] [Google Scholar]
- 18.EL-Latif AAA, Abd-El-Atty B, Venegas-Andraca SE, Mazurczyk W. Efficient quantum-based security protocols for information sharing and data protection in 5g networks. Future Gener. Computer Syst. 2019;100:893–906. doi: 10.1016/j.future.2019.05.053. [DOI] [Google Scholar]
- 19.Li D, et al. Discrete-time interacting quantum walks and quantum hash schemes. Quantum Inf. Process. 2013;12:1501–1513. doi: 10.1007/s11128-012-0421-8. [DOI] [Google Scholar]
- 20.Venegas-Andraca SE. Quantum walks: a comprehensive review. Quantum Inf. Process. 2012;11:1015–1106. doi: 10.1007/s11128-012-0432-5. [DOI] [Google Scholar]
- 21.Melnikov, A. A., Fedichkin, L. E. & Alodjants, A. Detecting quantum speedup by quantum walk with convolutional neural networks. arXiv preprint arXiv:1901.10632 (2019).
- 22.Zhang G. Quantum-inspired evolutionary algorithms: a survey and empirical study. J. Heuristics. 2011;17:303–351. doi: 10.1007/s10732-010-9136-0. [DOI] [Google Scholar]
- 23.Arrazola, J. M., Delgado, A., Bardhan, B. R. & Lloyd, S. Quantum-inspired algorithms in practice. arXiv preprint arXiv:1905.10415 (2019).
- 24.Montiel O, Rubio Y, Olvera C, Rivera A. Quantum-inspired acromyrmex evolutionary algorithm. Sci. Rep. 2019;9:1–10. doi: 10.1038/s41598-019-48409-5. [DOI] [PMC free article] [PubMed] [Google Scholar]
- 25.Yang Y-G, Pan Q-X, Sun S-J, Xu P. Novel image encryption based on quantum walks. Sci. Rep. 2015;5:7784. doi: 10.1038/srep07784. [DOI] [PMC free article] [PubMed] [Google Scholar]
- 26.Yang Y-G, Xu P, Yang R, Zhou Y-H, Shi W-M. Quantum hash function and its application to privacy amplification in quantum key distribution, pseudo-random number generation and image encryption. Sci. Rep. 2016;6:19788. doi: 10.1038/srep19788. [DOI] [PMC free article] [PubMed] [Google Scholar]
- 27.Abd-El-Atty B, EL-Latif AAA, Venegas-Andraca SE. An encryption protocol for NEQR images based on one-particle quantum walks on a circle. Quantum Inf. Process. 2019;18:272. doi: 10.1007/s11128-019-2386-3. [DOI] [Google Scholar]
- 28.EL-Latif, A. A. A., Abd-El-Atty, B., Abou-Nassar, E. M. & Venegas-Andraca, S. E. Controlled alternate quantum walks based privacy preserving healthcare images in internet of things. Optics & Laser Technology 105942 (2019).
- 29.EL-Latif, A. A. A., Abd-El-Atty, B. & Venegas-Andraca, S. E. Controlled alternate quantum walk-based pseudo-random number generator and its application to quantum color image encryption. Physica A: Statistical Mechanics and its Applications (2019).
- 30.EL-Latif AAA, Abd-El-Atty B, Venegas-Andraca SE. A novel image steganography technique based on quantum substitution boxes. Opt. Laser Technol. 2019;116:92–102. doi: 10.1016/j.optlastec.2019.03.005. [DOI] [Google Scholar]
- 31.Schmitz, A. T. Quantum walks: Theory, application, and implementation (2016).
- 32.Zeng M, Yong EH. Discrete-time quantum walk with phase disorder: localization and entanglement entropy. Sci. Rep. 2017;7:12024. doi: 10.1038/s41598-017-12077-0. [DOI] [PMC free article] [PubMed] [Google Scholar]
- 33.Souza A, Andrade R. Coin state properties in quantum walks. Sci. Rep. 2013;3:1976. doi: 10.1038/srep01976. [DOI] [PMC free article] [PubMed] [Google Scholar]
- 34.Wang, J. & Manouchehri, K. Physical implementation of quantum walks (Springer, 2013).
- 35.Du J, et al. Experimental implementation of the quantum random-walk algorithm. Phys. Rev. A. 2003;67:042316. doi: 10.1103/PhysRevA.67.042316. [DOI] [Google Scholar]
- 36.Douglas B, Wang J. Efficient quantum circuit implementation of quantum walks. Phys. Rev. A. 2009;79:052335. doi: 10.1103/PhysRevA.79.052335. [DOI] [Google Scholar]
- 37.Goyal SK, Roux FS, Forbes A, Konrad T. Implementation of multidimensional quantum walks using linear optics and classical light. Phys. Rev. A. 2015;92:040302. doi: 10.1103/PhysRevA.92.040302. [DOI] [Google Scholar]
- 38.Qiang X, et al. Efficient quantum walk on a quantum processor. Nat. Commun. 2016;7:11511. doi: 10.1038/ncomms11511. [DOI] [PMC free article] [PubMed] [Google Scholar]
- 39.Qi F, Wang Y, Ma Q, Zheng W. Experimentally simulating quantum walks with self-collimated light. Sci. Rep. 2016;6:28610. doi: 10.1038/srep28610. [DOI] [PMC free article] [PubMed] [Google Scholar]
- 40.Jeong Y-C, Di Franco C, Lim H-T, Kim M, Kim Y-H. Experimental realization of a delayed-choice quantum walk. Nat. Commun. 2013;4:2471. doi: 10.1038/ncomms3471. [DOI] [PubMed] [Google Scholar]
- 41.Lai, X. & Massey, J. L. A proposal for a new block encryption standard. In Workshop on the Theory and Application of of Cryptographic Techniques, 389–404 (Springer, 1990).
- 42.Zhang W, Pasalic E. Highly nonlinear balanced s-boxes with good differential properties. IEEE Trans. Inf. Theory. 2014;60:7970–7979. doi: 10.1109/TIT.2014.2360880. [DOI] [Google Scholar]
- 43.Blondeau C, Nyberg K. Perfect nonlinear functions and cryptography. Finite fields their Appl. 2015;32:120–147. doi: 10.1016/j.ffa.2014.10.007. [DOI] [Google Scholar]
- 44.Bicubic interpolation resize procedure, https://www.mathworks.com/help/matlab/ref/imresize.html (Accessed: 12-13-2019).
- 45.Yang Y-G, Zhao Q-Q. Novel pseudo-random number generator based on quantum random walks. Sci. Rep. 2016;6:20362. doi: 10.1038/srep20362. [DOI] [PMC free article] [PubMed] [Google Scholar]
- 46.Sipi image database-misc, http://sipi.usc.edu/database/database.php?volume=misc (Accessed: 7-22-2019).
- 47.Zhou Y, Cao W, Chen CP. Image encryption using binary bitplane. Signal. Process. 2014;100:197–207. doi: 10.1016/j.sigpro.2014.01.020. [DOI] [Google Scholar]
- 48.Tsafack N, et al. Design and implementation of a simple dynamical 4-d chaotic circuit with applications in image encryption. Inf. Sci. 2020;515:191–217. doi: 10.1016/j.ins.2019.10.070. [DOI] [Google Scholar]
- 49.Nestor T, et al. A multidimensional hyperjerk oscillator: Dynamics analysis, analogue and embedded systems implementation, and its application as a cryptosystem. Sens. 2020;20:83. doi: 10.3390/s20010083. [DOI] [PMC free article] [PubMed] [Google Scholar]
- 50.Chiang, C.-F., Nagaj, D. & Wocjan, P. Efficient circuits for quantum walks. arXiv preprint arXiv:0903.3465 (2009).
- 51.Genske M, et al. Electric quantum walks with individual atoms. Phys. Rev. Lett. 2013;110:190601. doi: 10.1103/PhysRevLett.110.190601. [DOI] [PubMed] [Google Scholar]
- 52.Alvarez G, Li S. Some basic cryptographic requirements for chaos-based cryptosystems. Int. J. Bifurc. chaos. 2006;16:2129–2151. doi: 10.1142/S0218127406015970. [DOI] [Google Scholar]
- 53.Melnikov AA, Fedichkin LE. Quantum walks of interacting fermions on a cycle graph. Sci. Rep. 2016;6:34226. doi: 10.1038/srep34226. [DOI] [PMC free article] [PubMed] [Google Scholar]
- 54.Li D, Yang Y-G, Bi J-L, Yuan J-B, Xu J. Controlled alternate quantum walks based quantum hash function. Sci. Rep. 2018;8:225. doi: 10.1038/s41598-017-18566-6. [DOI] [PMC free article] [PubMed] [Google Scholar]
- 55.Yang Y-G, Bi J-L, Li D, Zhou Y-H, Shi W-M. Hash function based on quantum walks. Int. J. Theor. Phys. 2019;58:1861–1873. doi: 10.1007/s10773-019-04081-z. [DOI] [Google Scholar]
- 56.Yang Y-G, et al. Simple hash function using discrete-time quantum walks. Quantum Inf. Process. 2018;17:189. doi: 10.1007/s11128-018-1954-2. [DOI] [Google Scholar]
- 57.Cao W-F, et al. Constructing quantum hash functions based on quantum walks on johnson graphs. Quantum Inf. Process. 2018;17:156. doi: 10.1007/s11128-018-1923-9. [DOI] [Google Scholar]
- 58.El-Latif, A. A. A. et al. Secret images transfer in cloud system based on investigating quantum walks in steganography approaches. Physica A: Statistical Mechanics and its Applications 123687 (2019).
- 59.Li D, Zhang J, Ma X-W, Zhang W-W, Wen Q-Y. Analysis of the two-particle controlled interacting quantum walks. Quantum Inf. Process. 2013;12:2167–2176. doi: 10.1007/s11128-012-0516-2. [DOI] [Google Scholar]
- 60.Zhou Y, Bao L, Chen CP. A new 1d chaotic system for image encryption. Signal. Process. 2014;97:172–182. doi: 10.1016/j.sigpro.2013.10.034. [DOI] [Google Scholar]
- 61.Belazi A, El-Latif AAA. A simple yet efficient s-box method based on chaotic sine map. Opt. 2017;130:1438–1444. [Google Scholar]
- 62.Khan M, Asghar Z. A novel construction of substitution box for image encryption applications with gingerbreadman chaotic map and s 8 permutation. Neural Comput. Appl. 2018;29:993–999. doi: 10.1007/s00521-016-2511-5. [DOI] [Google Scholar]
- 63.Wang Y, Wong K-W, Li C, Li Y. A novel method to design s-box based on chaotic map and genetic algorithm. Phys. Lett. A. 2012;376:827–833. doi: 10.1016/j.physleta.2012.01.009. [DOI] [Google Scholar]
- 64.Tang G, Liao X, Chen Y. A novel method for designing s-boxes based on chaotic maps. Chaos, Solitons Fractals. 2005;23:413–419. doi: 10.1016/j.chaos.2004.04.023. [DOI] [Google Scholar]
- 65.Özkaynak F, Çelik V, Özer AB. A new s-box construction method based on the fractional-order chaotic chen system. Signal, Image Video Process. 2017;11:659–664. doi: 10.1007/s11760-016-1007-1. [DOI] [Google Scholar]
- 66.Belazi A, Khan M, El-Latif AAA, Belghith S. Efficient cryptosystem approaches: S-boxes and permutation–substitution-based encryption. Nonlinear Dyn. 2017;87:337–361. doi: 10.1007/s11071-016-3046-0. [DOI] [Google Scholar]
- 67.Hussain I, Shah T, Gondal MA. A novel approach for designing substitution-boxes based on nonlinear chaotic algorithm. Nonlinear Dyn. 2012;70:1791–1794. doi: 10.1007/s11071-012-0573-1. [DOI] [Google Scholar]